The End of Aadhaar Photocopies: A Preview of UIDAI’s Evolving Verification Flows
Aadhaar verification in India has shifted from using physical copies to a digital, consent-driven model. This new approach minimizes data exposure, ensures accountability, and aligns with UIDAI and DPDP principles.
For several years, Aadhaar usage in the Indian economy has been a catalyst for enhanced identity verification; however, one could argue that it has operated in a compliance grey zone.
While regulated entities adopted UIDAI-approved authentication and eKYC mechanisms, many non-regulated and semi-regulated sectors, including hospitality, workforce onboarding, residential access management, and assisted service environments, continued to rely on the collection of physical Aadhaar copies.
This practice persisted due to the absence of viable digital alternatives. However, it has increasingly conflicted with both the Aadhaar Act and the principles now codified under the Digital Personal Data Protection (DPDP) Act.
Recent UIDAI changes signal a clear regulatory direction: identity verification must be accountable, consent-driven, and data-minimised regardless of sector.
Regulatory Intent: From Informal Practices To Accountable Verification
Historically, only regulated entities were permitted to access formal Aadhaar authentication rails. Other sectors verified identity without standardized digital mechanisms, often storing physical documents without defined retention policies or audit trails.
UIDAI’s requirement for registration of entities seeking Aadhaar-based verification addresses this gap directly.
The underlying principle is straightforward: If an entity verifies identity using Aadhaar, it must be able to demonstrate lawful purpose, user consent, and appropriate data handling.
This has immediate implications for:
- Hospitality and lodging providers
- Workforce and gig platforms
- Residential and corporate access systems
- Fallback journeys for regulated entities
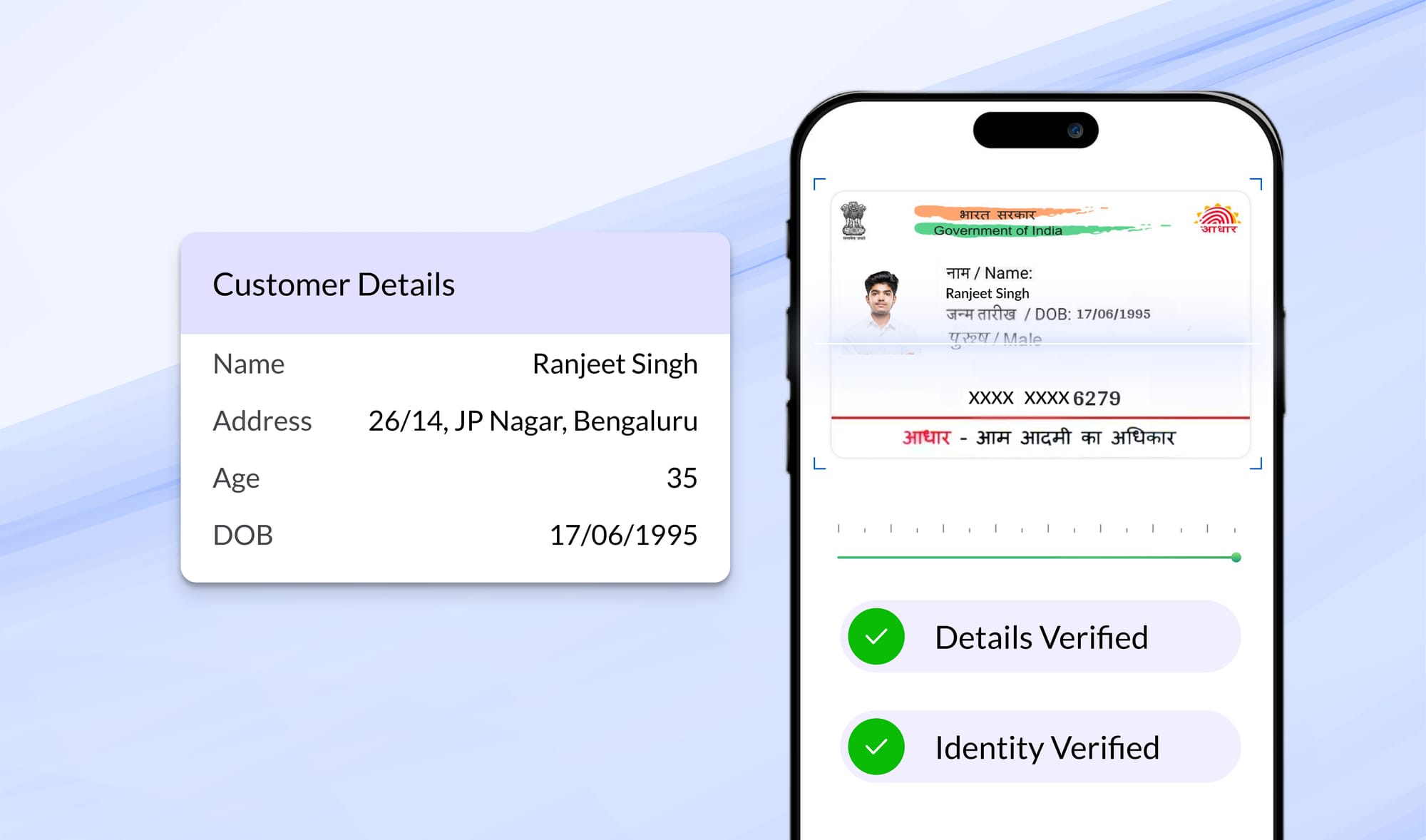
Why Physical Aadhaar Copies Are A Compliance Risk
From a compliance perspective, Aadhaar photocopies introduce three systemic risks.
1. Excessive Data Collection: Photocopies expose full Aadhaar numbers, complete addresses, and dates of birth, even when such data is not necessary for the stated purpose. This directly contradicts data minimisation principles under DPDP.
2. Indefinite Retention: Physical documents are rarely subject to defined retention or deletion schedules. This creates uncontrolled long-term exposure without a lawful basis for continued storage.
3. Lack of Auditability: Paper-based verification provides no reliable mechanism to demonstrate when consent was obtained, what data was accessed, or who accessed it.
In regulatory terms, the issue is not merely security. It is an inability to demonstrate compliance.
UIDAI’s Emerging Model: Verification Without Data Retention
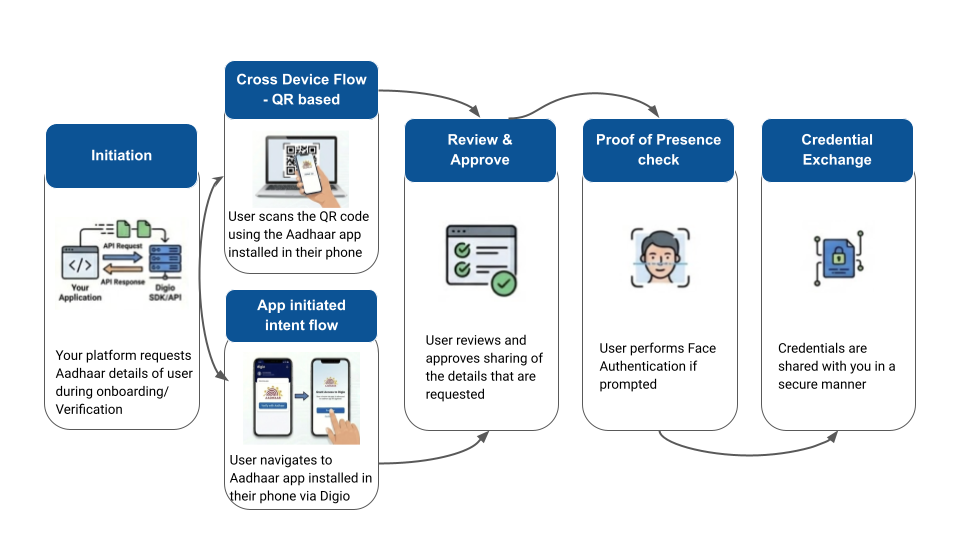
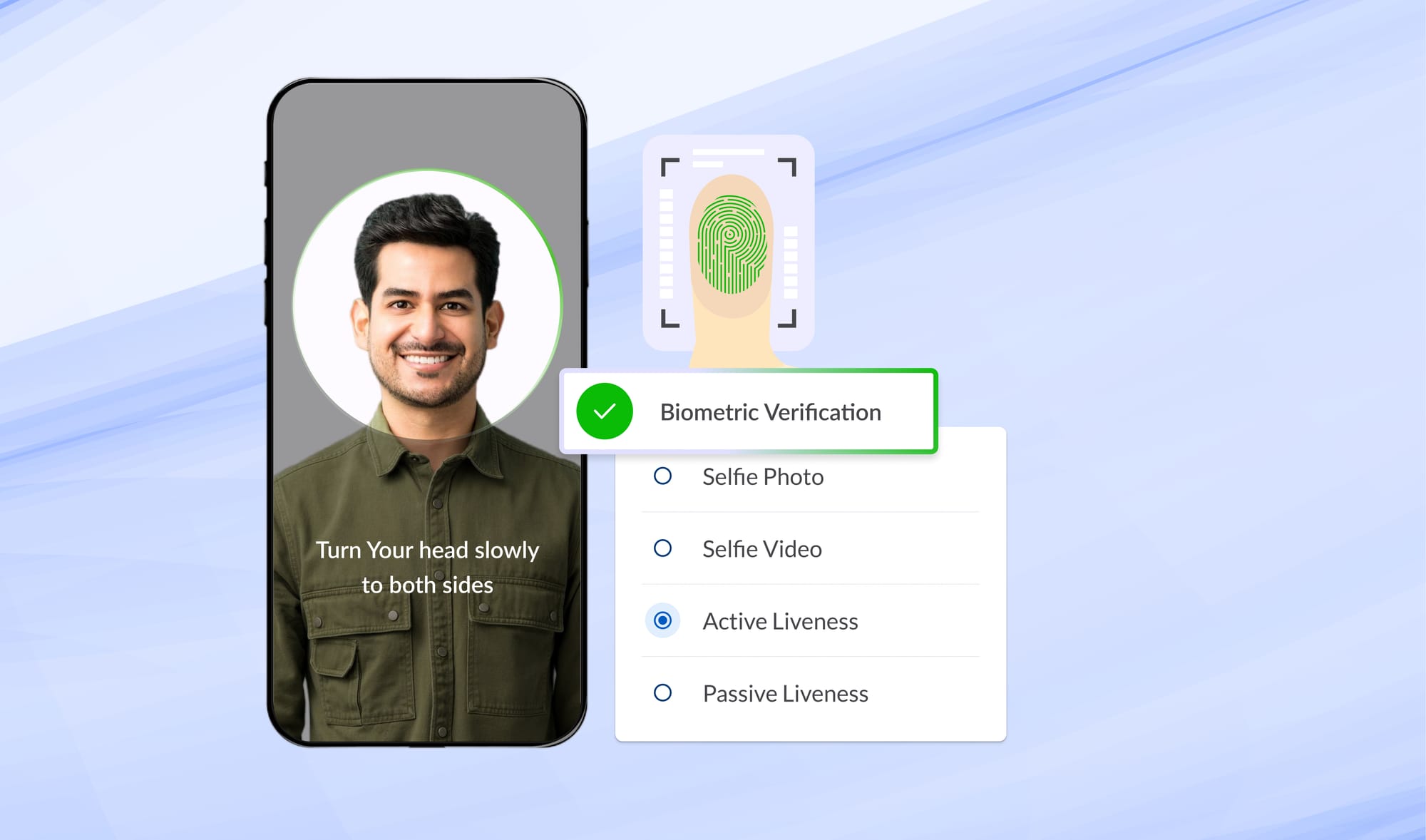
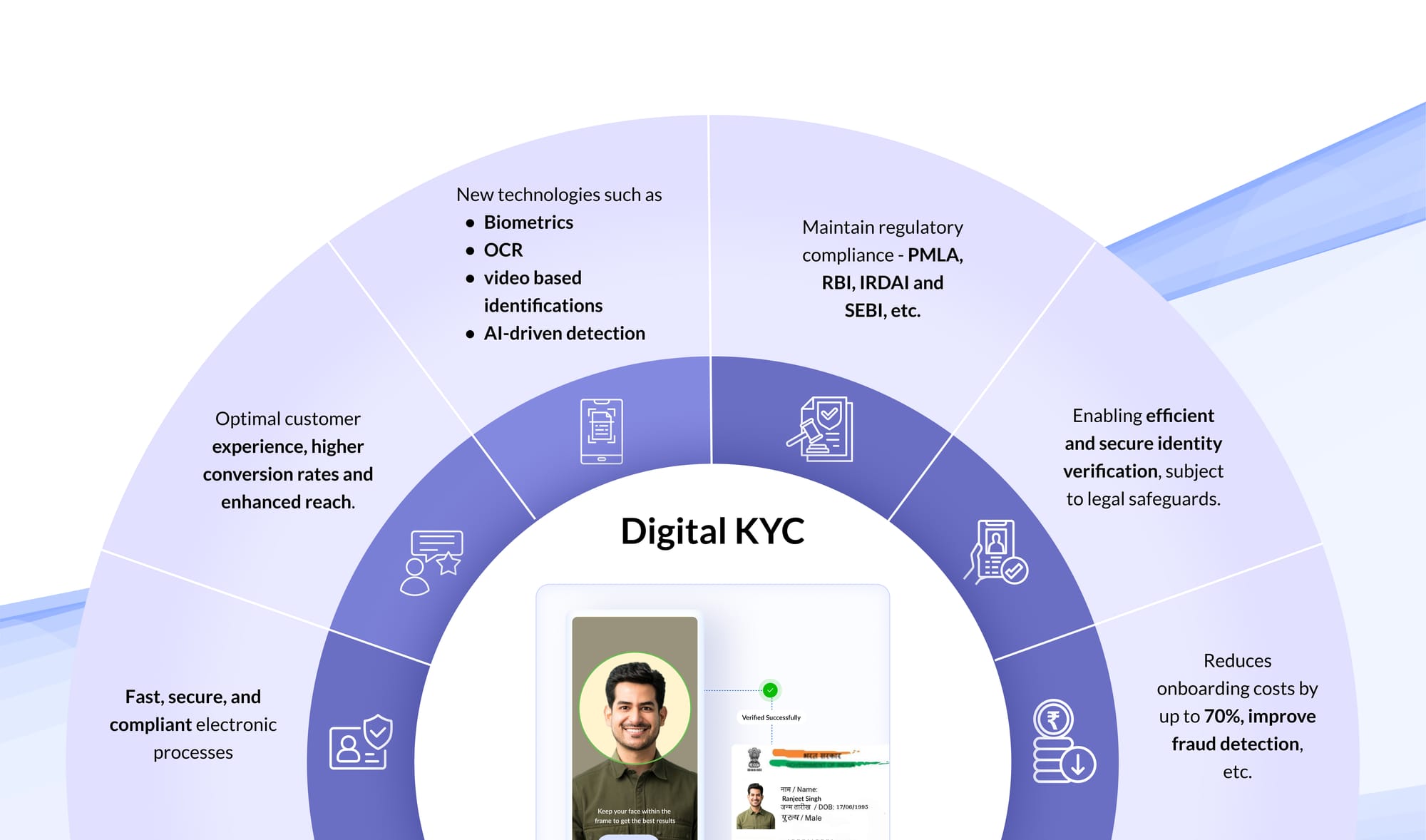
UIDAI’s shift toward QR-based and Aadhaar-app–mediated credential sharing introduces a verification model that aligns more closely with modern privacy and compliance requirements.
Under this model:
- Identity data is shared only with explicit user consent
- Credentials are digitally signed and tamper-proof
- Aadhaar numbers are not disclosed
- Verification can occur without persistent storage of identity documents
The verifier confirms authenticity and validity at the point of interaction, without creating a long-lived repository of personal data.
This represents a move from document collection to claim validation.
Key Features
Selective Disclosure
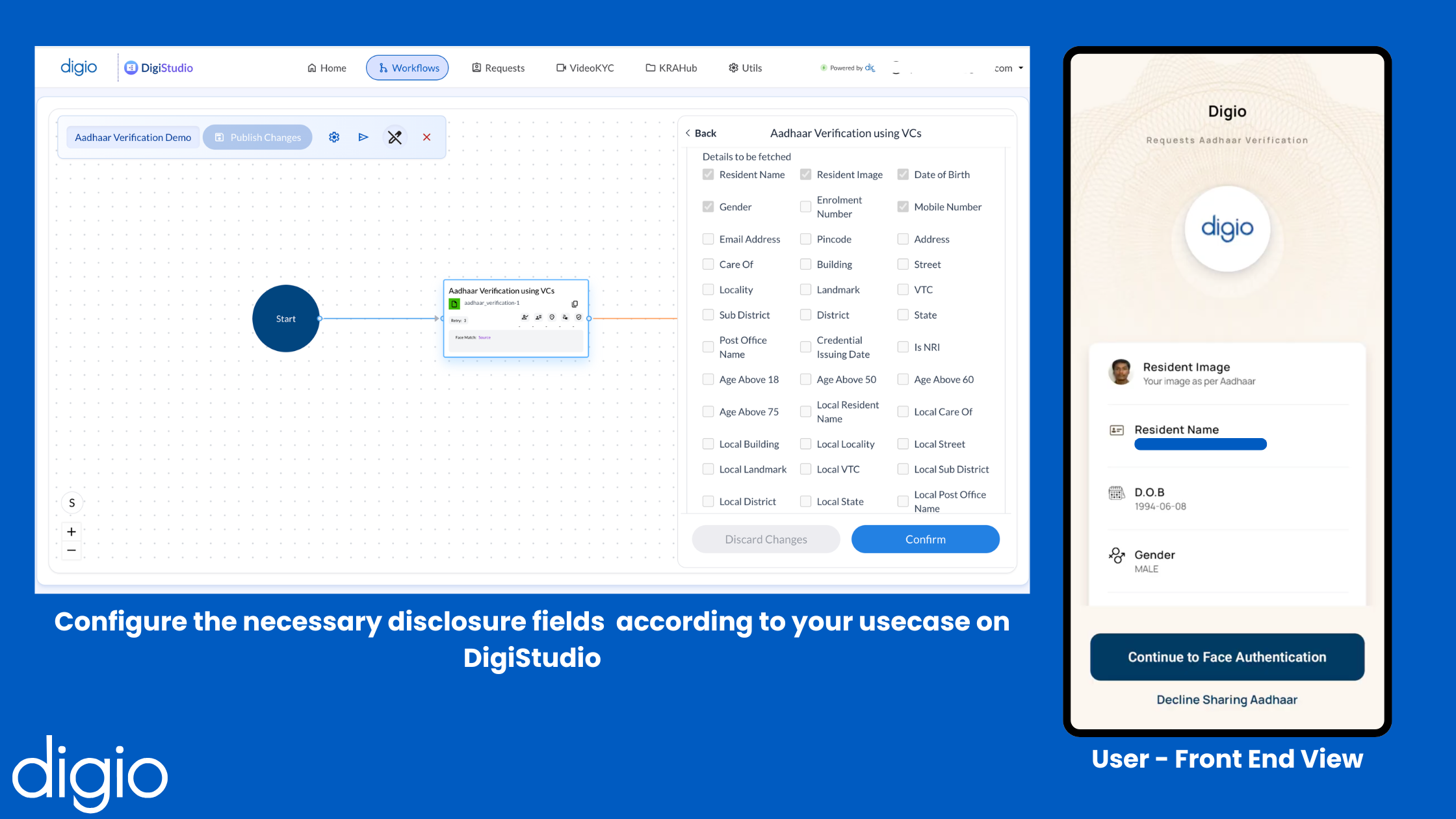
Verification requests can be limited to fields that are strictly necessary for the stated purpose. For example, a verifier may request only name and photograph, without receiving the address or Aadhaar number.
This supports both purpose limitation and data minimisation obligations.
Zero-Knowledge Attribute-Level Verification
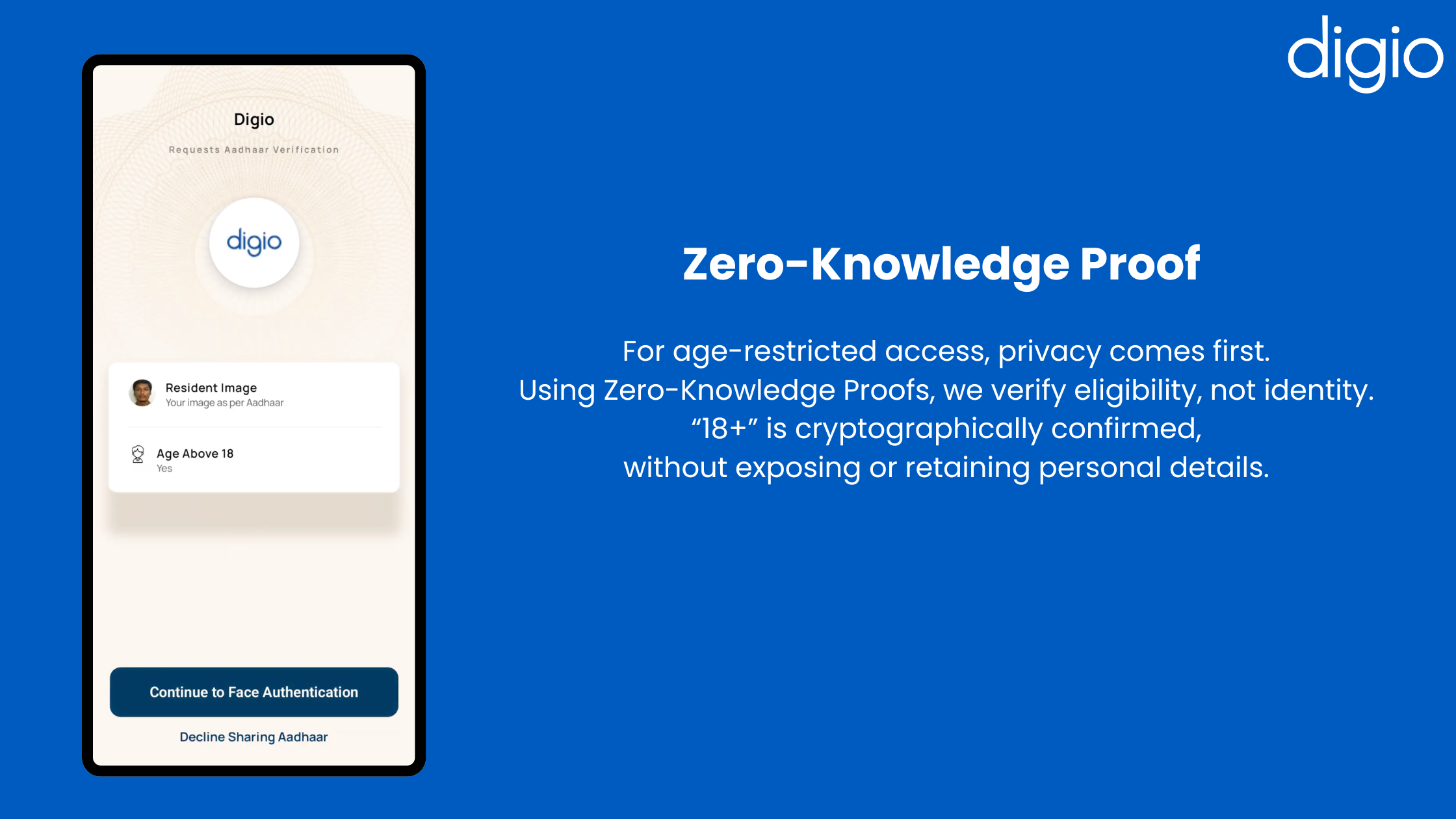
In certain cases, even raw personal data is unnecessary. Verification may instead require confirmation of a condition, such as whether an individual is above a certain age or qualifies under a specific residency category.
In these scenarios, the system can return a signed assertion confirming the condition without disclosing the underlying personal data used to derive it.
From a compliance standpoint, this reduces exposure while still meeting verification requirements.
Applicability Across Sectors
While hospitality is often cited due to the prevalence of photocopy collection, the compliance benefits extend further.
- Workforce and gig onboarding: reduces document storage risk while maintaining identity assurance
- Access control environments: enable verification without maintaining physical ID logs
- Financial services: usable as a supplementary or fallback verification layer, like when an OTP cannot be delivered, without replacing mandated eKYC processes
The Role of Orchestration and Auditability
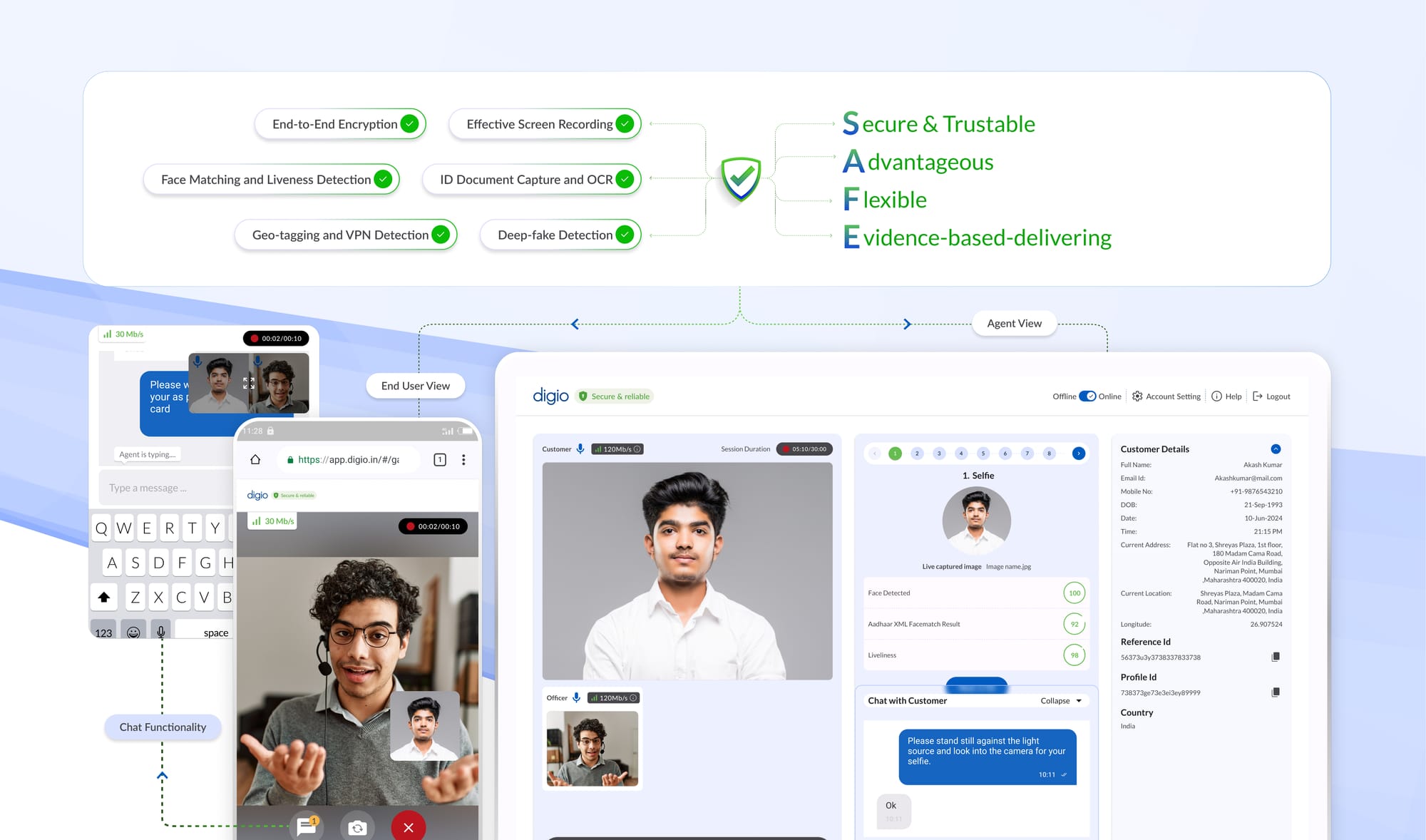
From a compliance perspective, the effectiveness of any verification method depends on how well it is operationalised.
Key requirements include:
- Standardised request generation
- Explicit, recorded user consent
- Time-stamped verification records
- Clear separation between verification and storage
- Documented fallback mechanisms
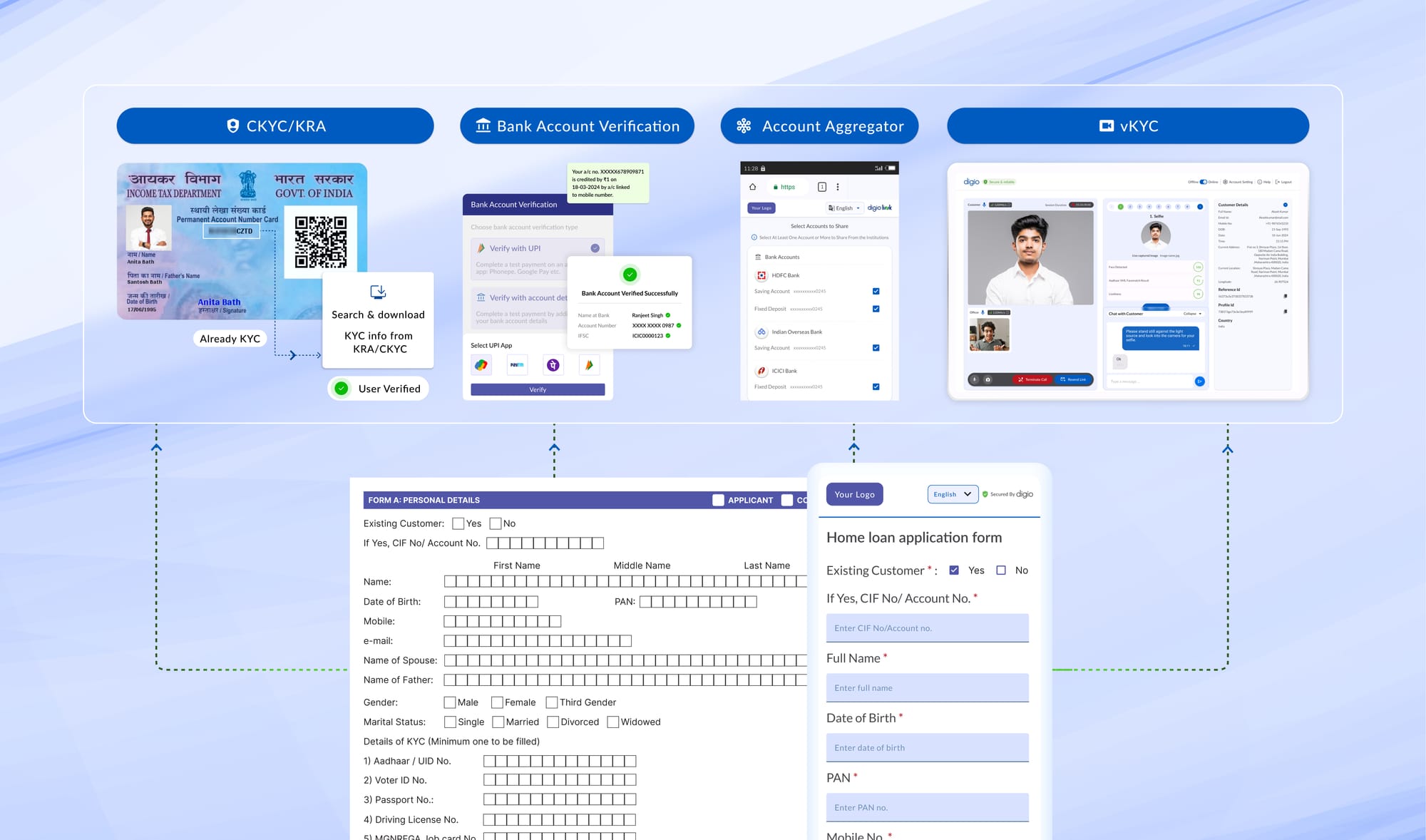
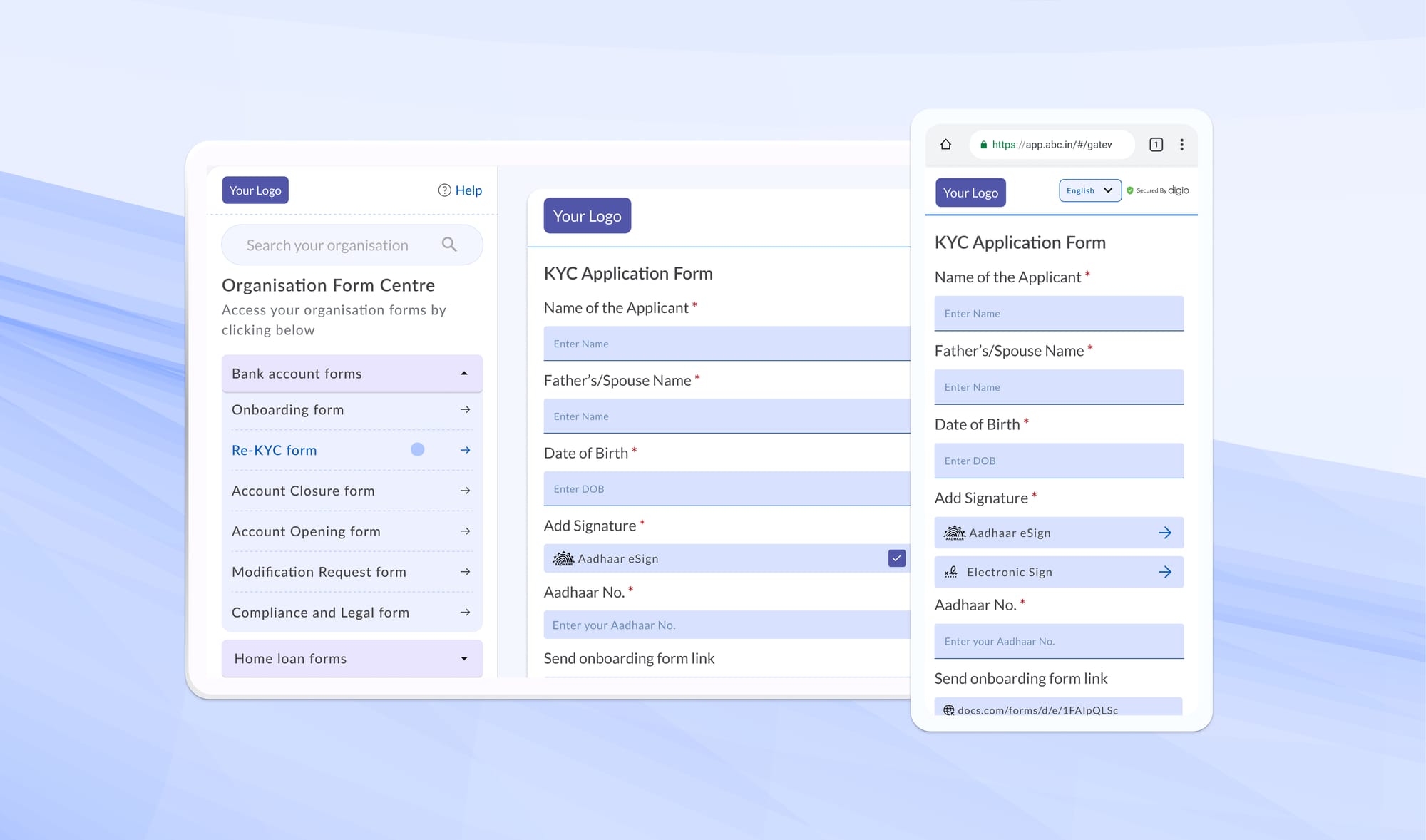
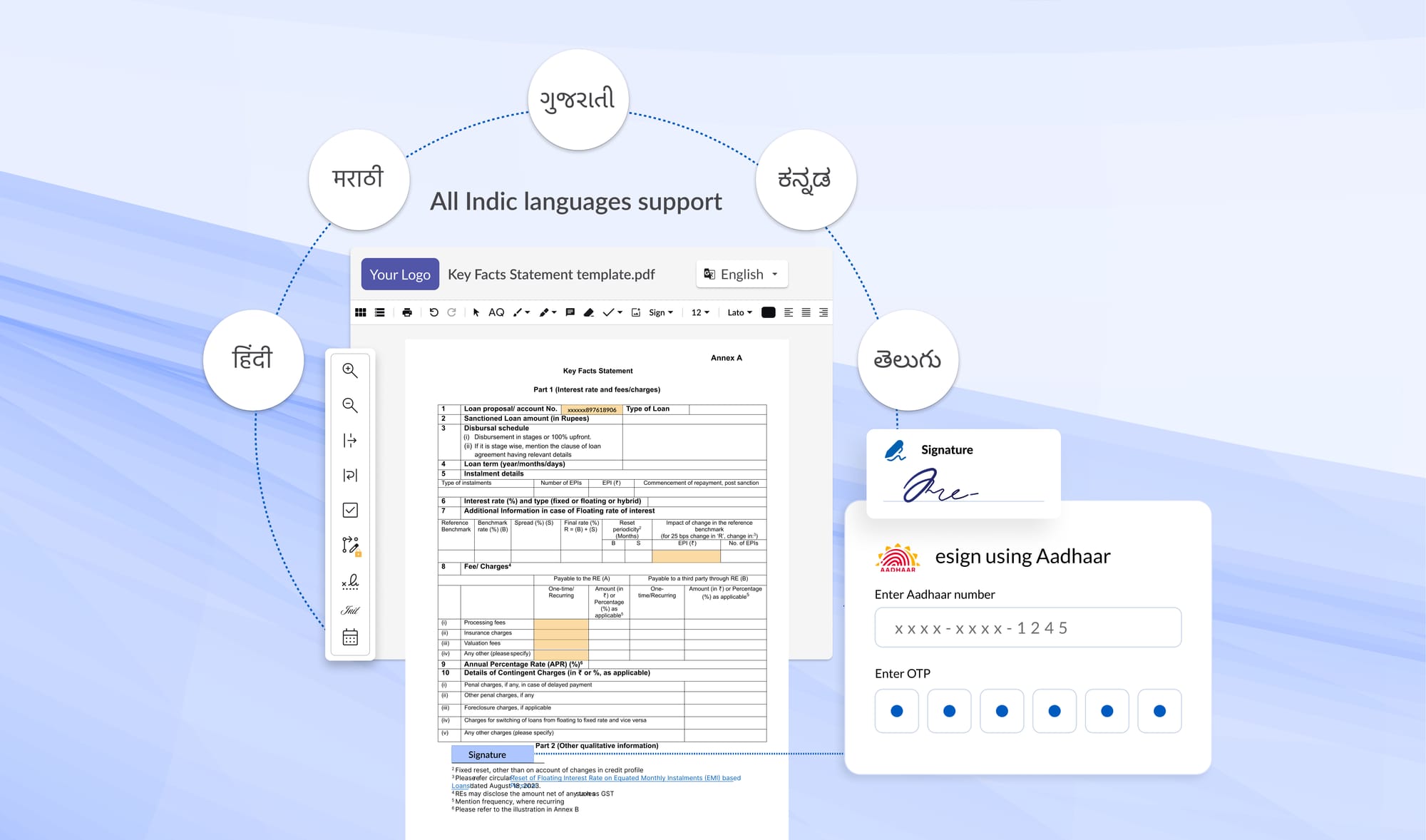
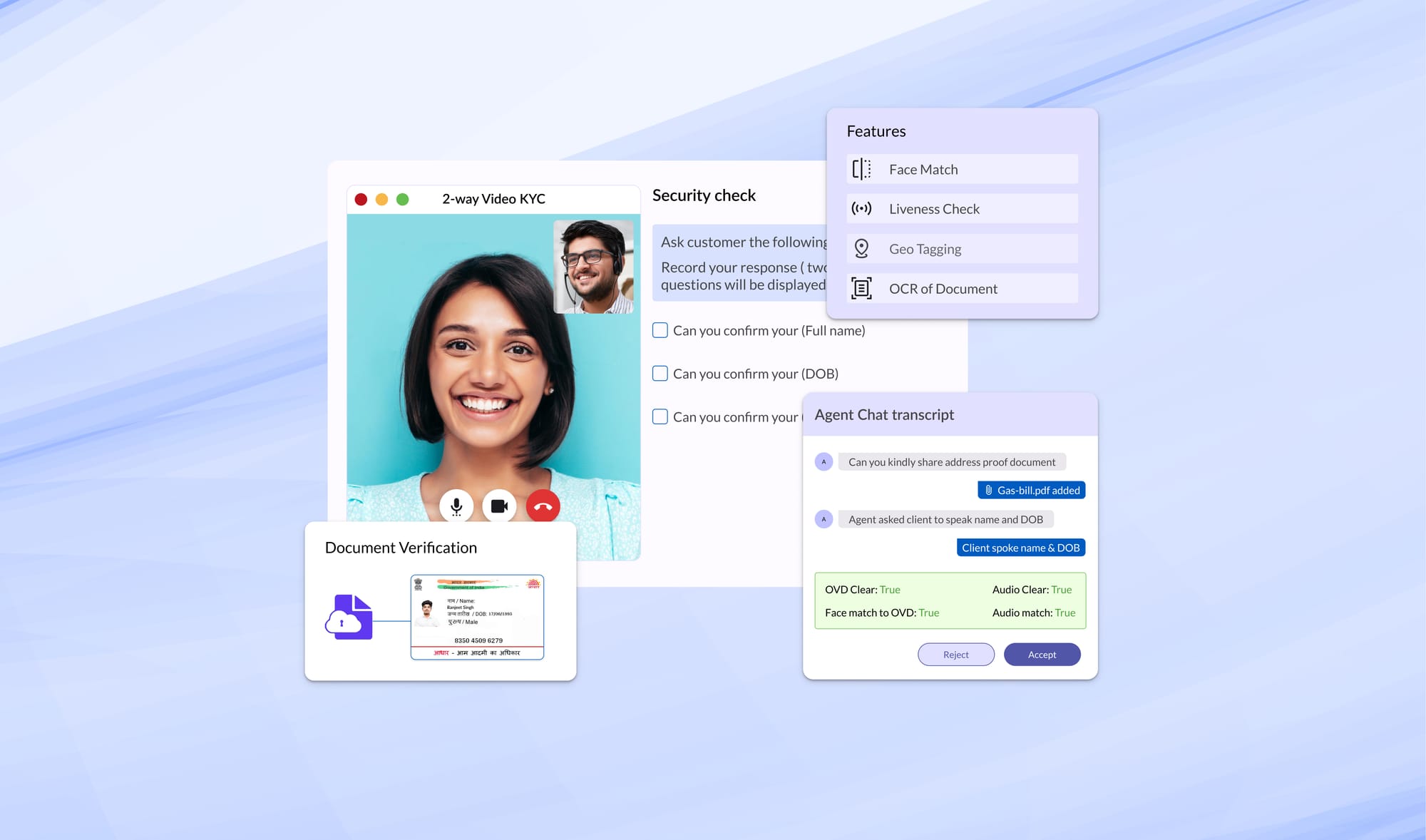
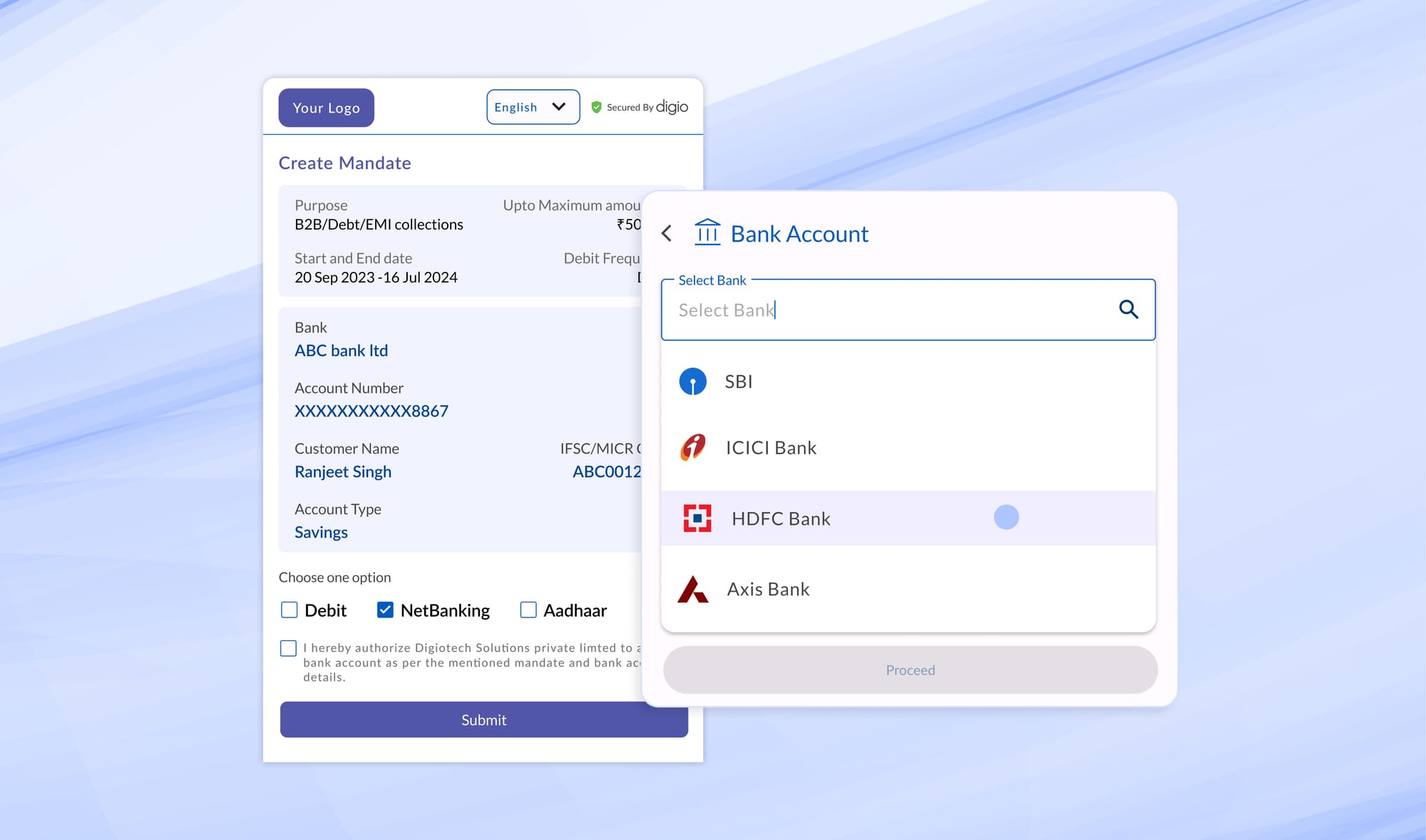
Platforms such as Digio’s DigiKYC are designed to address these requirements by serving as an orchestration layer that manages verification flows, validates credentials, maintains audit logs, and supports alternate verification modes when required.
The regulatory direction is clear: identity verification must minimise data exposure while maximising accountability.
Physical Aadhaar copies fail this test on multiple fronts. App-based, consent-driven verification mechanisms offer a path forward that aligns with both UIDAI guidance and DPDP principles.
Read more Blogs
Digitally transform business operations with Digio!
Try first. Subscribe later.
Boost your legal ops efficiency by 80%
Learn how Digio can enhance your business productivity
Get 1-on-1 business use case solutioning
Speak with our business consultants to get a solution walkthrough for your business requirement
Test the APIs
Let your development team test our API suite to understand configurability and product integration
Subscribe
Get the best in industry commercials for your business usecase