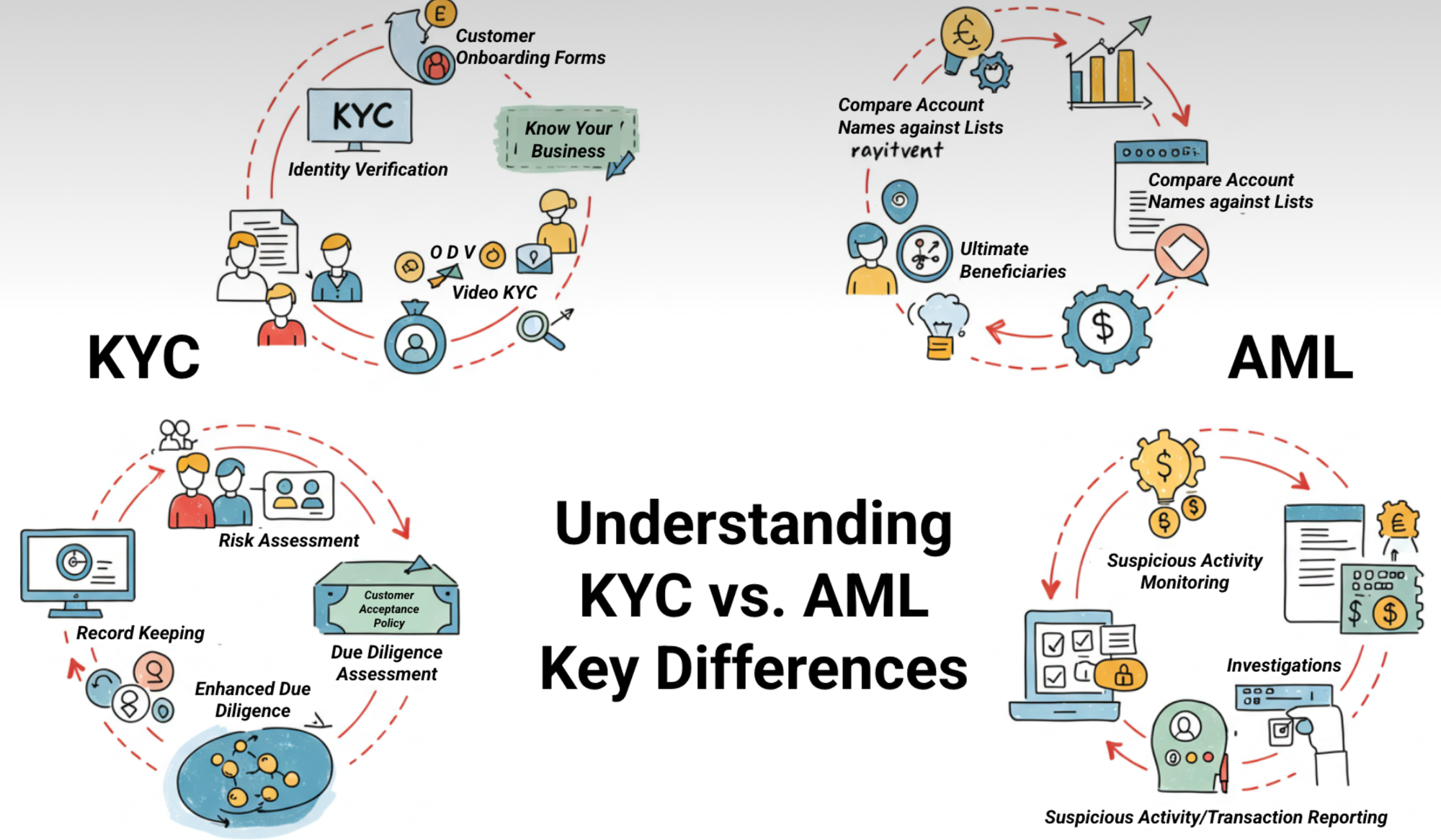
Understanding KYC vs. AML: Key Differences
KYC vs. AML, although they work hand-in-hand, each has its own scope, timing, and technical requirements. This article focuses on a concise breakdown to help businesses assess solutions against both requirements while remaining compliant.
When evaluating compliance platforms, it’s crucial to distinguish Know Your Customer (KYC)—the identity-verification engine—from Anti-Money Laundering (AML)—the ongoing surveillance framework. Though they work hand-in-hand, each has its own scope, timing, and technical needs.
Below is a concise breakdown to help businesses assess solutions against both requirements.
1. Definitions and Purpose
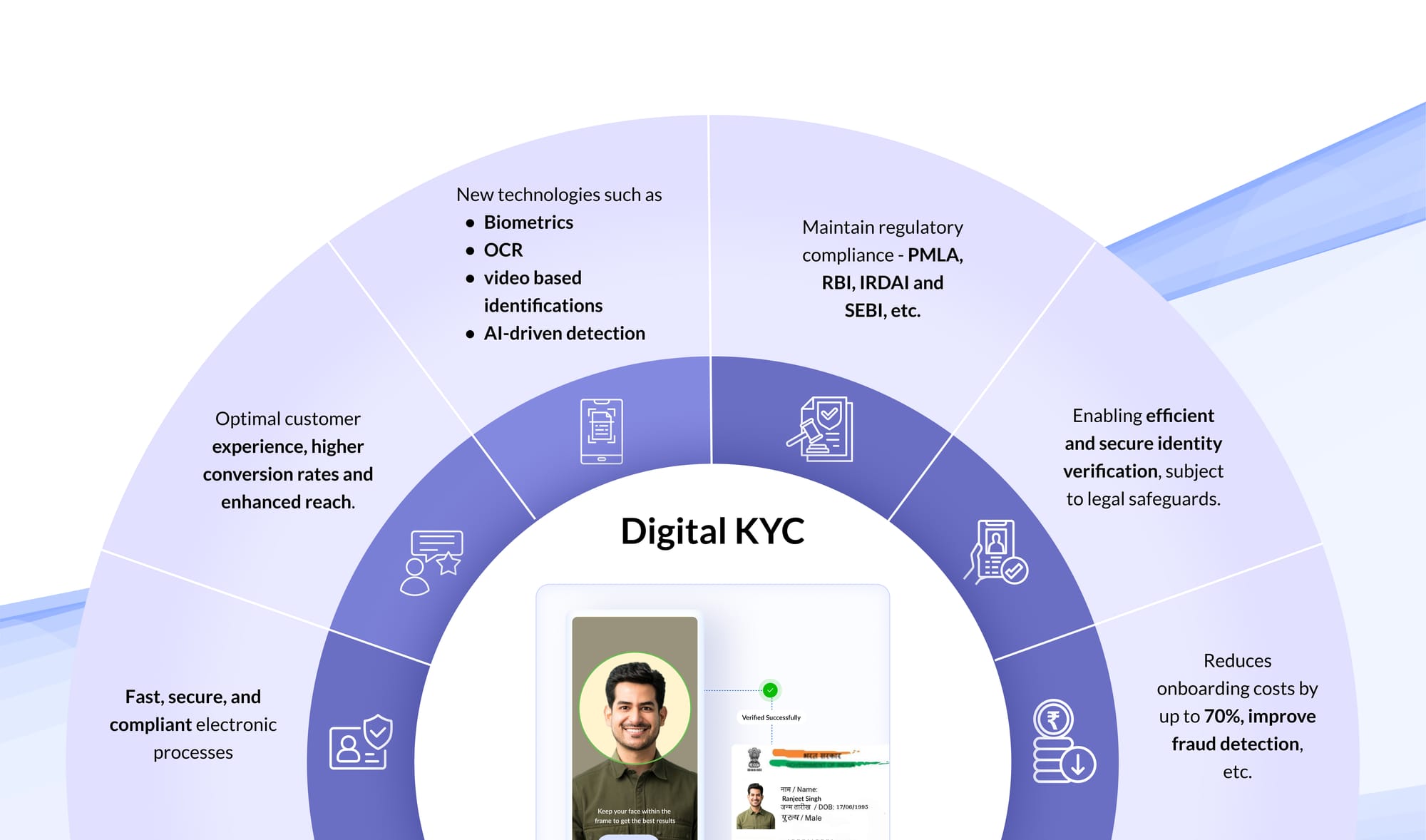
- KYC verifies who your users are at account opening (and periodically). It establishes identity, captures baseline risk attributes, and ensures you only onboard legitimately documented customers.
- AML monitors what your users do after onboarding: screening them and every transaction they make against sanctions/PEP lists, flagging suspicious patterns, and managing regulatory reporting.
Together, KYC and AML form the foundation of a compliant, risk-focused enterprise.
Neglect one, and the other’s effectiveness crumbles.
2. Scope and Timing
3. Core Activities
KYC
- Customer Acceptance Policy (CAP): Define which customer profiles you’ll serve (e.g., retail investors, lending borrowers).
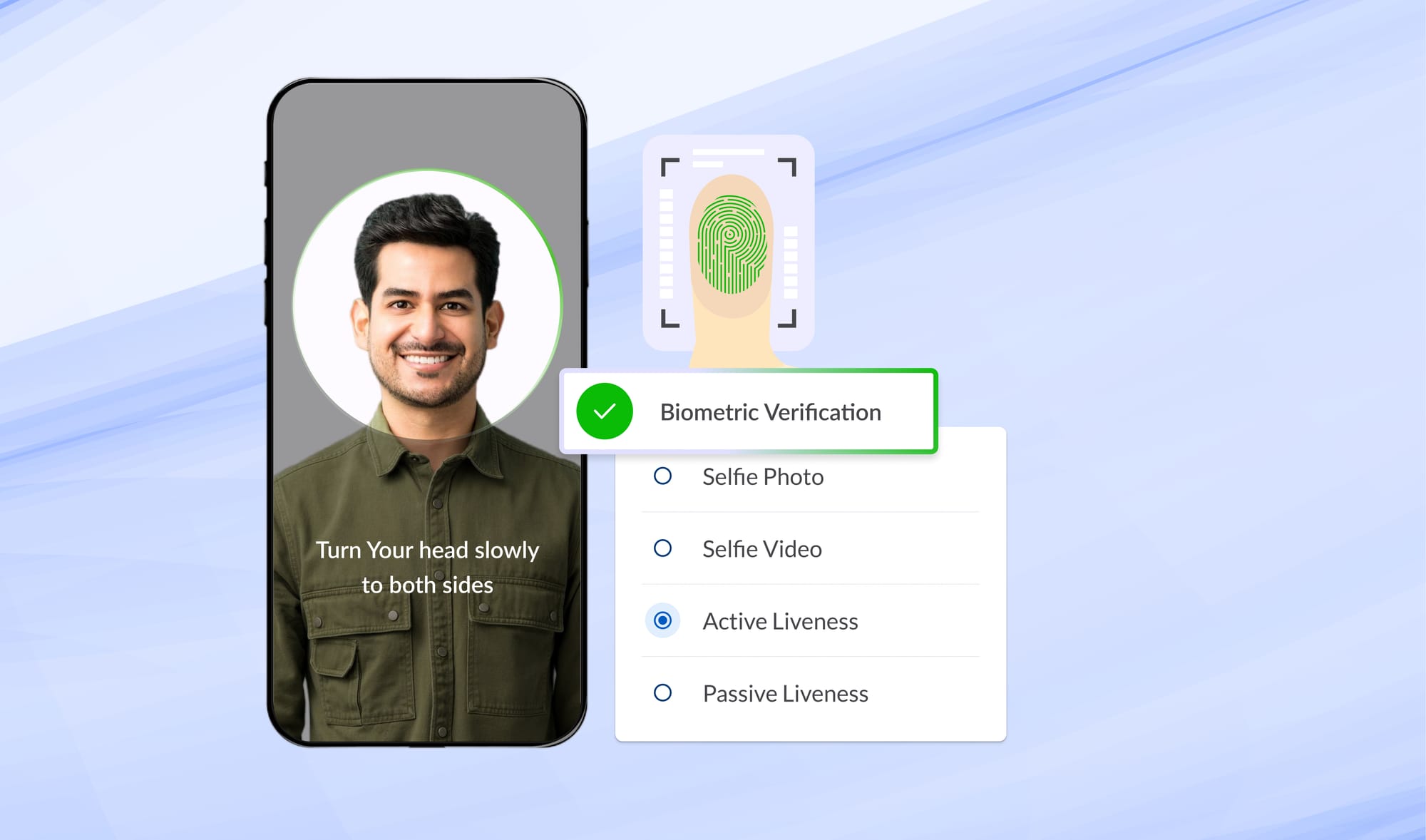
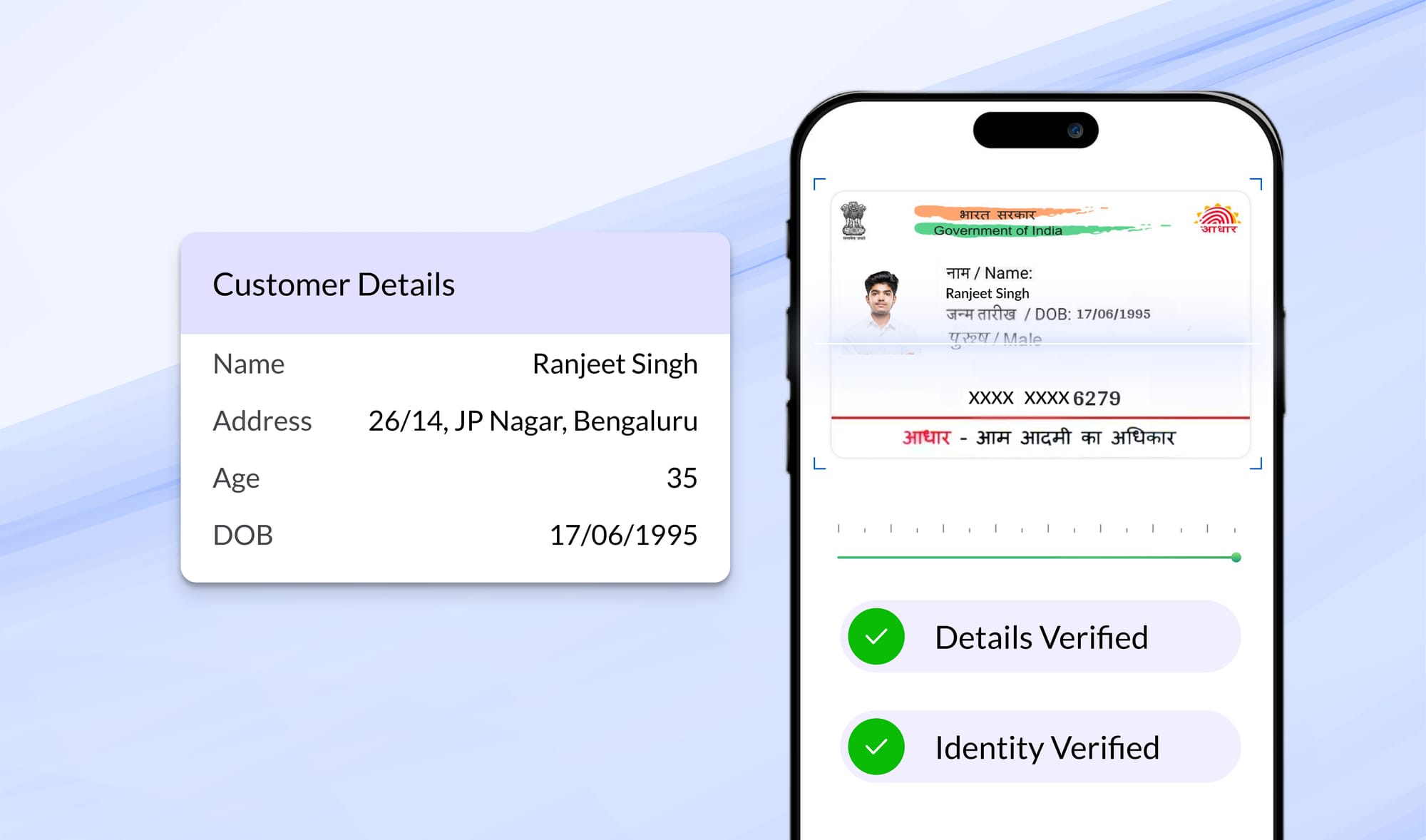
- Customer Identification Procedures (CIP): Verify ID documents (Aadhaar, Passport, PAN) and conduct biometric liveness checks.
- Customer Due Diligence (CDD): Assign a risk rating (low/medium/high) based on factors like geography, occupation, and transaction intent.
- Record Retention: Store KYC records for at least five years post-closure.
AML
- Watchlist Screening: Continuously match customers against updated sanctions, PEP, and adverse-media databases.
- Transaction Monitoring: Apply static rules (transaction velocity checks, geolocation mismatches) alongside machine-learning models that learn normal behaviour and flag anomalies.
- Alert Investigation & STR Filing: Investigate true positives and file Suspicious Transaction Reports with FIU-IND within seven days of forming suspicion.
- Audit Trails & Governance: Log every screening decision, rule change, and investigation note in an immutable ledger for regulator inspections.
4. Why Both Matter and Why You Can’t Shortcut Either
- Skipping rigorous KYC undermines your ability to assess customer risk. If identities aren’t verified, even the best AML engine can’t reliably interpret behaviour.
- Weak AML controls mean illicit flows could slip through despite strong KYC. Criminals often exploit “clean” accounts via transaction layering or sudden high-value moves.
For compliance teams, the mandate is clear: use a compliance stack that delivers both robust KYC and comprehensive AML, without introducing bottlenecks to onboarding or transaction speeds.
5. Evaluating a Unified Solution
When you compare vendors, ensure they satisfy both KYC and AML criteria:
- Onboarding Performance
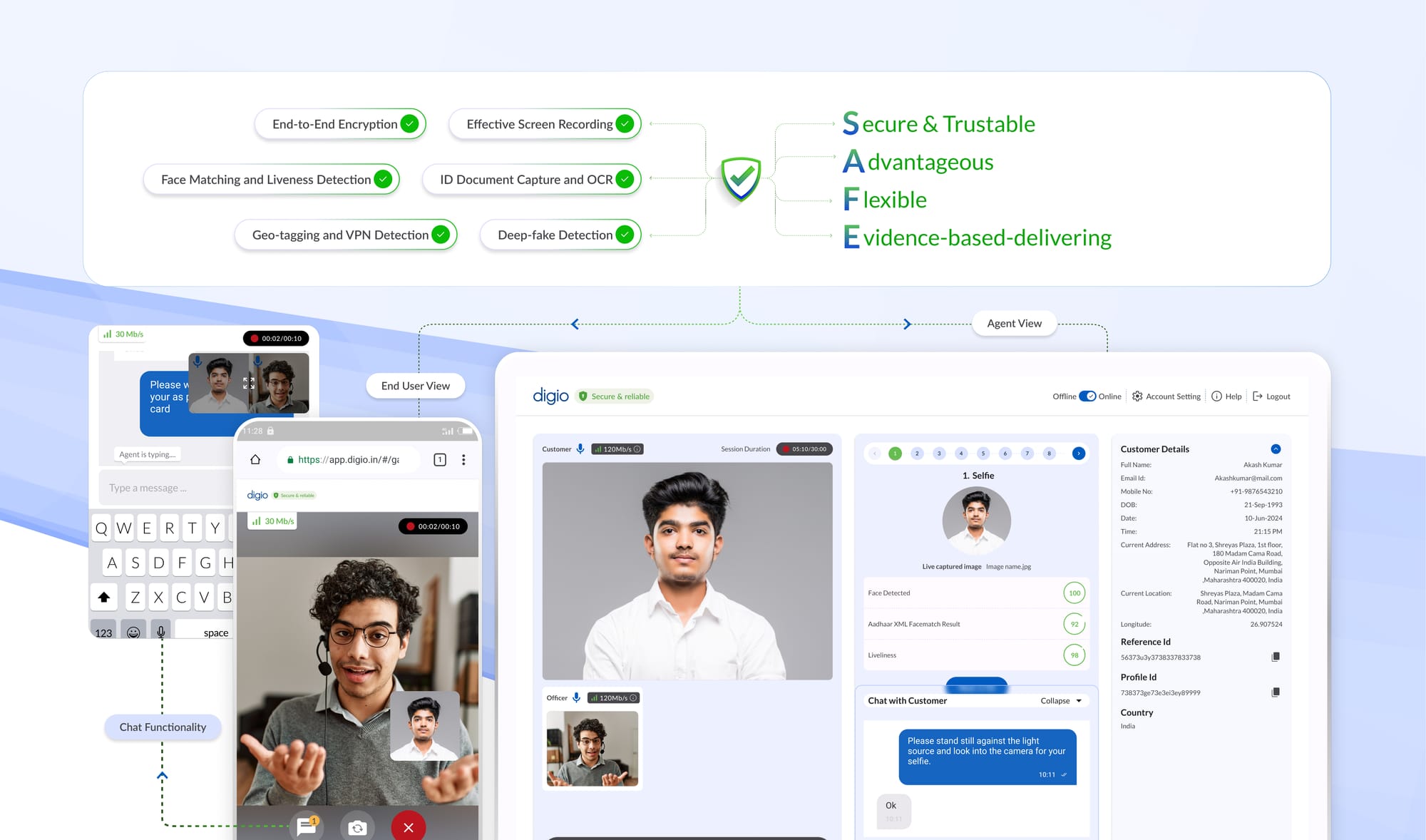
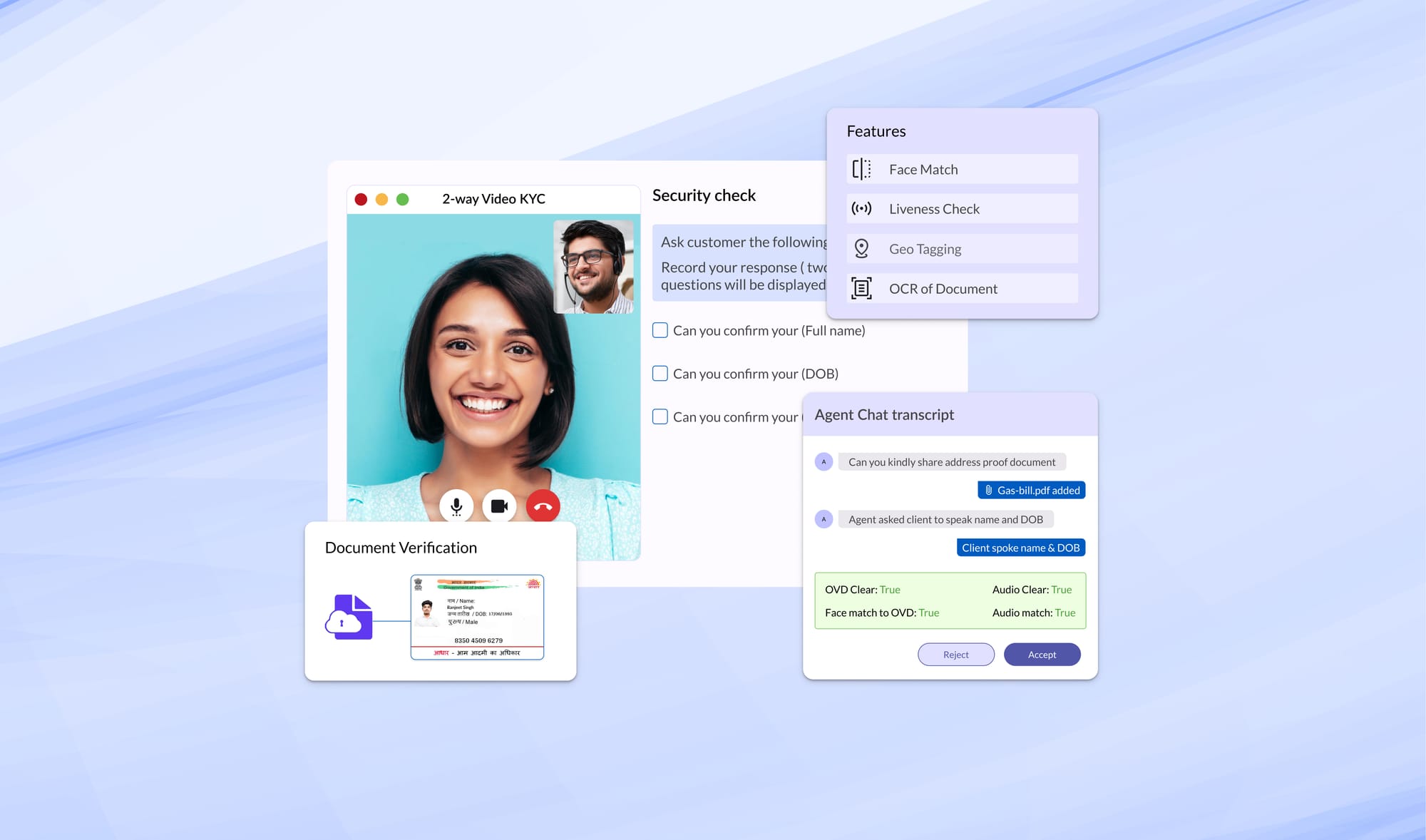
- Seamless e-KYC authentication, OCR document parsing, and biometric liveness checks.
- Parallel watchlist screening to avoid sequential delays.
- Flexible Rule Management
- Low-code/no-code interface for both KYC risk thresholds and AML transaction rules.
- Sandbox back-testing against historical data to calibrate false-positive rates.
- Scalability & Throughput
- Low Screening latency per fuzzy-match, auto-scaling to handle seasonal spikes.
- Caching and parallel pipelines to minimize redundant checks.
- False-Positive Control
- ML-driven filters that suppress near-duplicates and low-risk mismatches.
- Transparent alert RCAs so investigators understand “why” a case surfaced.
- End-to-End Monitoring & Re-Screening
- On-time ingestion of large transaction feeds.
- Periodic re-screening of existing customers against updated watchlists and media feeds.
- Automated Reporting & Audit Readiness
- Built-in STR workflows with pre-populated templates and deadline reminders.
- Immutable audit logs are accessible for internal/external audits and supervisory reviews.
6. How Digio Addresses Both
Digio exemplifies a unified approach:
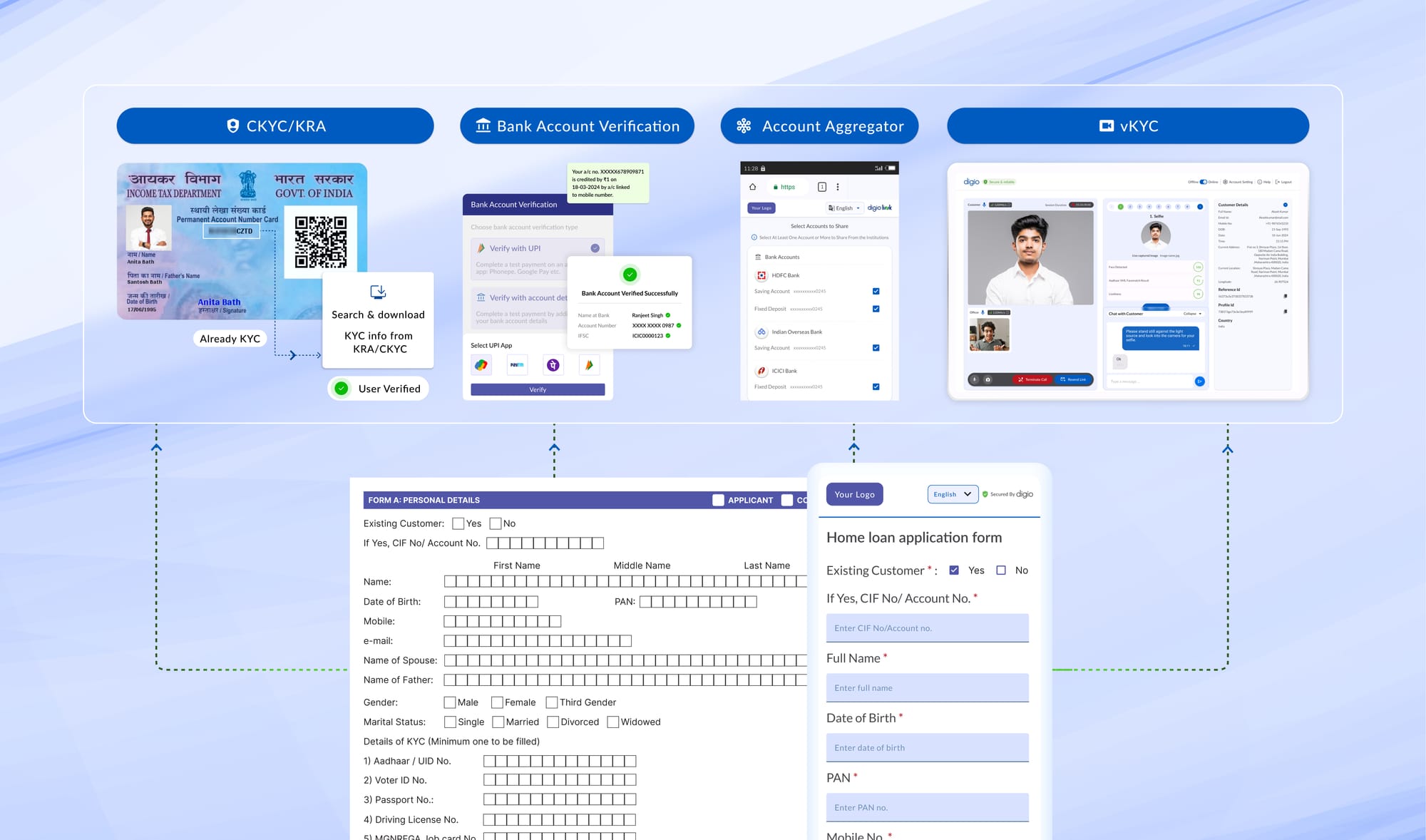
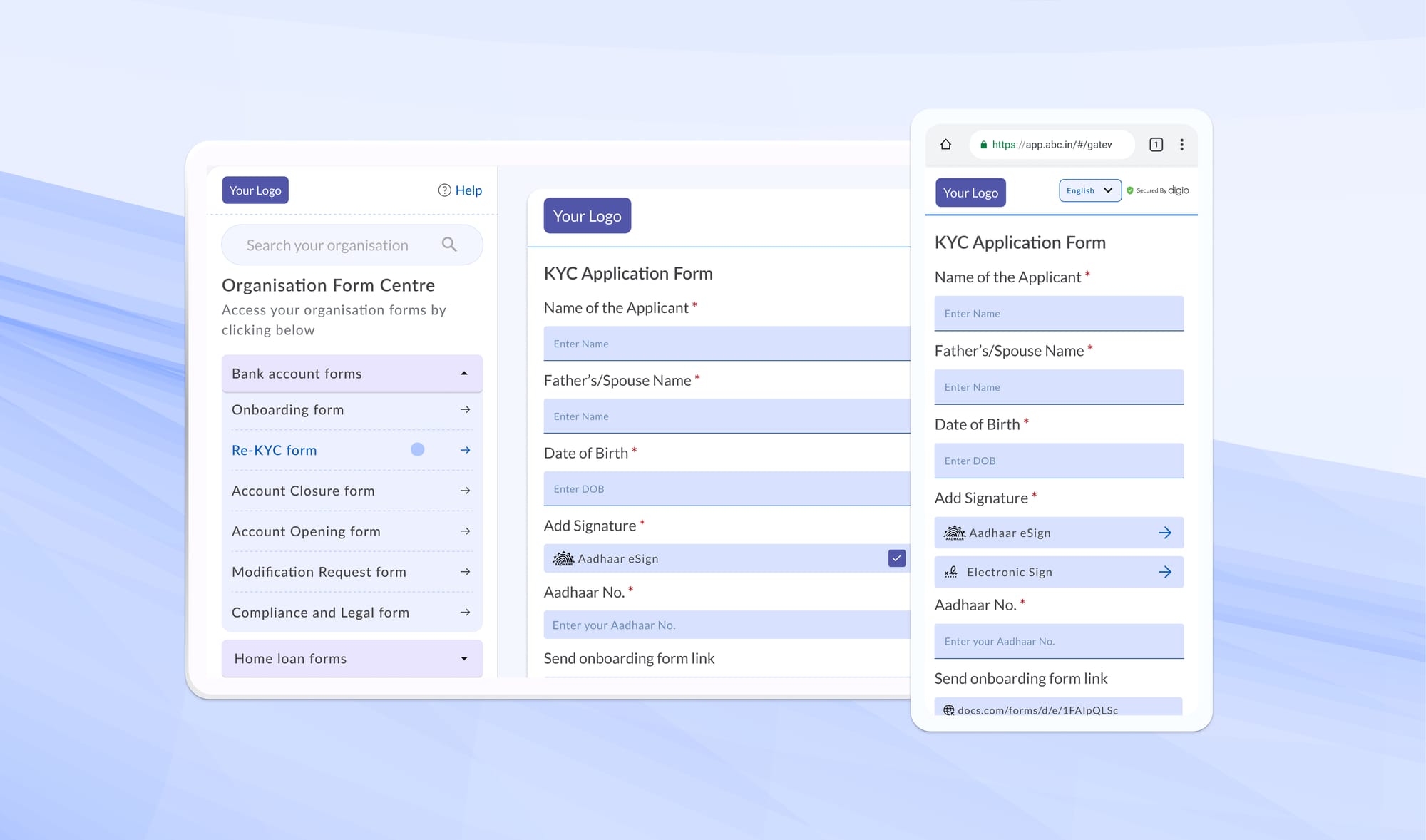
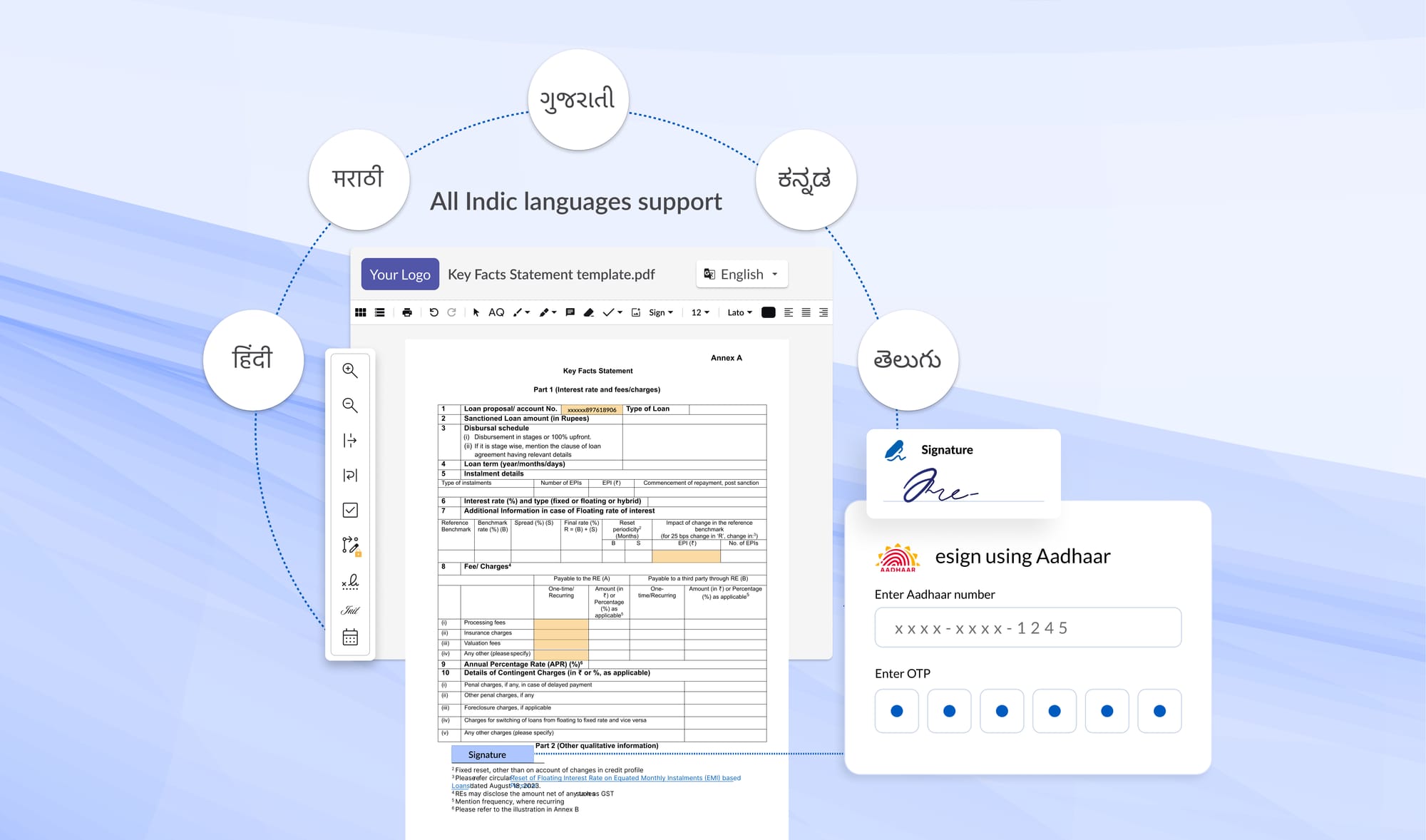
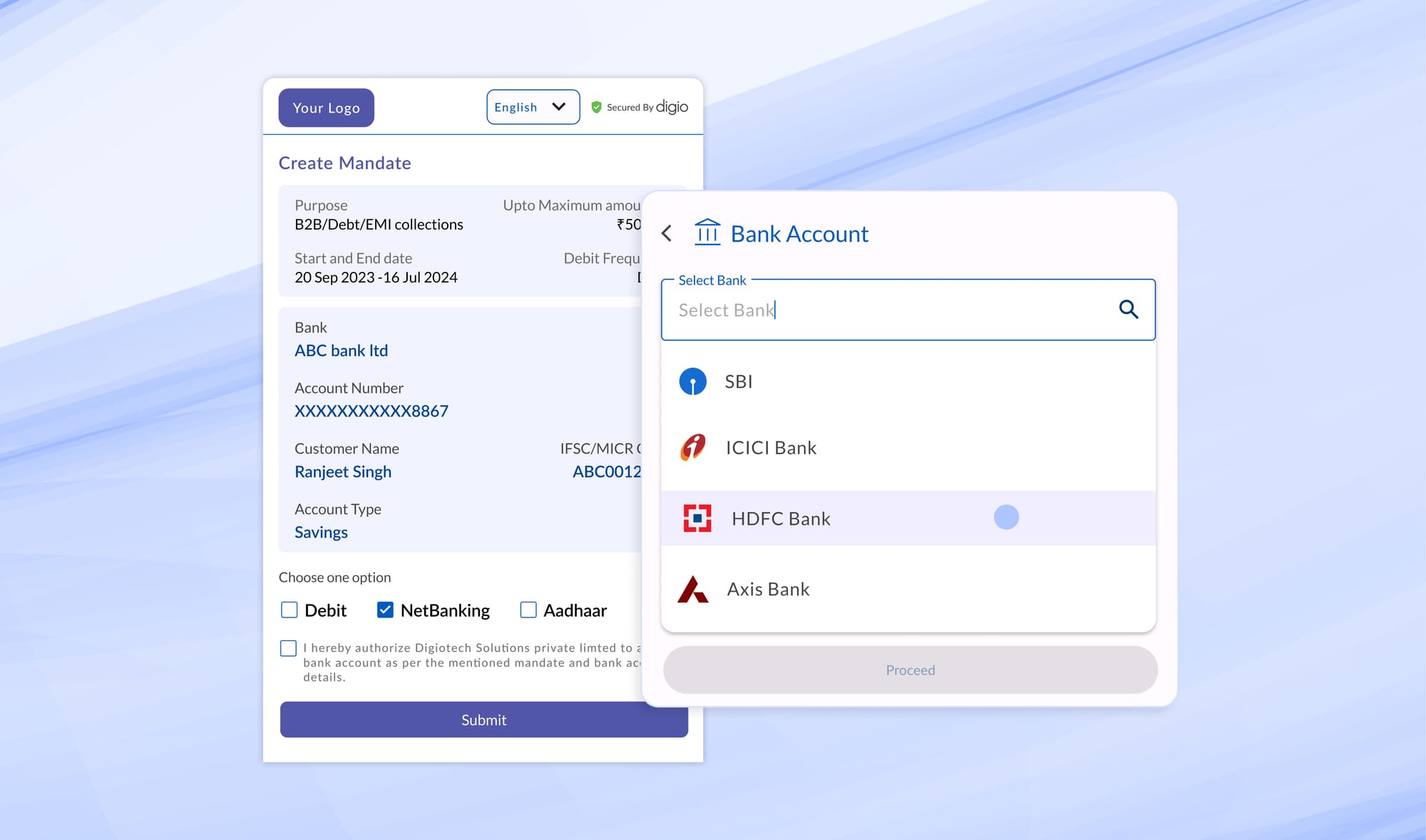
- Integrated KYC APIs: Aadhaar e-KYC, document OCR, DigiLocker, and selfie liveness checks, plus immediate screen-upon-onboarding against global sanctions and PEP lists.
- Rule Orchestrator: Simplified no-code solutions for defining, testing, and publishing both KYC and AML rules, no engineering tickets needed.
- High-Speed Screening Engine: 50-100ms per fuzzy match at enterprise scale, ensuring no onboarding or transaction backlogs.
- Continuous Surveillance: Live transaction feeds, hybrid detection models, and automated re-screening.
- Compliance Automation: STR filing, submission tracking, and tamper-proof logs keep you audit-ready and regulator-confident.
KYC and AML are distinct but inseparable elements of a resilient compliance framework. As a business, you must evaluate solutions with integrated end-to-end coverage: from identity checks to transaction surveillance and simplified regulatory filings. Using a single vendor not only reduces integration complexity but also ensures your risk and product teams can innovate rapidly, ensuring both KYC and AML guardrails scale with your business.
Read more Blogs
Digitally transform business operations with Digio!
Try first. Subscribe later.
Boost your legal ops efficiency by 80%
Learn how Digio can enhance your business productivity
Get 1-on-1 business use case solutioning
Speak with our business consultants to get a solution walkthrough for your business requirement
Test the APIs
Let your development team test our API suite to understand configurability and product integration
Subscribe
Get the best in industry commercials for your business usecase