Beyond Consent Management: Addressing DPDPA Compliance Comprehensively
India's DPDPA marks a pivotal step in reinforcing data privacy standards and fostering trust between organisations and their users. Digio.in & Aurva have partnered to deliver value to businesses, as they navigate the complexities involved in this entire journey.
The Evolving Landscape of Data Protection
India's Digital Personal Data Protection Act (DPDPA) marks a pivotal step in reinforcing data privacy standards and fostering trust between organizations and their users. In keeping with established DEPA framework, the Act incorporates the concept of "Consent Manager" as a custodian for streamlining the management of user consents across various digital platforms.
While this approach has been incorporated to ensure standardization, our experience indicates that in its current state, it could also introduce some challenges. In certain scenarios, the approach may create additional friction rather than simplifying consent management. Therefore, as organizations work toward DPDP compliance, a more comprehensive DPDP strategy that effectively balances robust data privacy measures with practical consent management is essential.
What is a Consent Manager?
The DPDPA defines a Consent Manager as "a person registered with the Board, who acts as a single point of contact to enable a Data Principal to give, manage, review and withdraw consent through an accessible, transparent and interoperable platform." This definition seems promising at first glance, suggesting a centralized solution for consent management that could simplify the user experience.
However, when evaluated technically, the Consent Manager model presents significant challenges from multiple perspectives:
For Data Principals (Users):
- Potential confusion from having to interact with multiple Consent Managers to manage their data privacy
- Fragmentation of consent across different platforms due to the above
- Unclear cost structures and value propositions - No clarity on consent management being a B2C or B2B proposition
- Fiduciary Integration delays that could span years - as seen with FIPs(data custodian) in the Account Aggregator ecosystem
For the Consent Manager:
- Need to integrate with thousands of Data Fiduciaries to be meaningful to citizens
- Absence of standardized interoperability protocols unlike UPI among the consent managers
- Risk of becoming obsolete if they are unable to ensure enforcement of data subject rights (Rights of citizens to access, correct or erase their data)
- Substantial regulatory compliance burden if not integrated with backend systems holding PII data
For Data Fiduciaries (Organizations):
- Limited perceived value while still needing to maintain internal consent systems
- Integration complexity with multiple Consent Managers as seen with FIPs in the ecosystem
- Potential confusion from parallel consent tracks
- Heavy regulatory penalties on inadequate consent governance protocols
Learning from the Account Aggregator Framework
The Account Aggregator (AA) framework, the first of its kind consent manager for financial data sharing, left us with some fundamental learnings on implementing privacy systems at scale
- Robust Data Foundations:Many financial institutions faced integration delays due to disparate legacy systems and the lack of a unified, regulator-driven customer data processing framework across their financial offerings.
- Fragmented User Experience: Despite centralized infrastructure and standardized protocols, users encounter disjointed experiences due to issues like inconsistent FIP uptime, varying FIP coverage across AAs, and no interoperability designed among AAs.
- Clear Purpose Mapping: Legacy organizations often lacked documentation on why specific data was collected, which hampered their ability to build valuable use cases and effectively participate in the ecosystem.
- Ongoing Customer Education: Beyond clear consent screens, persistent education is needed so users fully understand what data is shared, why, and for how long, ensuring they are truly informed.
- Operational Readiness: Organizations that conducted comprehensive data assessments and establish governance frameworks before implementation achieved compliance more efficiently than those focusing solely on technical integration.
With experience in regulatory compliance and managing millions of data records as a technical solutions provider, we understand the challenges businesses face in comprehending their exposure to PII data, we see DPDP compliance beyond just consent management:
1) The Foundation : Data Security
Before organizations can effectively manage consent, they must first establish robust data privacy management. This includes:
Data Discovery
Organizations must know what data they possess and where it resides. Without this foundational knowledge, consent management becomes impossible. Many organizations struggle with fragmented data repositories across departments, cloud services, and legacy systems.
Data Classification
Not all data requires the same level of protection. Proper classification enables organizations to apply appropriate controls based on sensitivity and regulatory requirements. This is particularly important for personal data under DPDP.
Data Flow Monitoring and Data Lineage
Understanding how data flows through systems is crucial for both compliance and effective consent management. Organizations must track data from collection to processing to deletion, ensuring transparency throughout the lifecycle.
Data Access Management (DAM)
Controlling who can access what data is essential for maintaining data confidentiality and integrity. Fine-grained access controls that align with consent parameters are required.
External Flow Monitoring
Continuously monitor data shared with third parties and external data processors to ensure complete visibility into outbound data flows. Track sensitive data exchanges in real time to prevent unauthorized sharing and enforce data localization policies, ensuring no sensitive data leaves the country.
PII Vault
Protect PII and sensitive data and govern their flow across the entire technology stack with governing policies and granular access controls while keeping the data encrypted at rest, in transit, and in memory.
2) GRC Management : Data Governance
Post establishing firm foundation on data privacy operations, it becomes imperative to establish the confidentiality, integrity, and accessibility of data
Incident Response & Breach Notification: Detection and containment of breaches with automated response workflows, integrated with robust notification channels. Requires clear escalation paths, root-cause analysis, and remediation tracking.
Encryption & Access Control: End-to-end encryption for data at rest and in transit, robust identity & access management, and multi-factor authentication. Enforcement of least-privilege principles across all data assets.
Data Minimization
Implement policies ensuring only essential data is collected and stored for the minimum period required. Must support automated data purging and compliance with DPDPA’s data minimization principles.
Regulatory Reporting & Audit Readiness
Generation of compliance reports, impact assessments (DPIA), and support for data protection impact assessments and legal obligations. Must integrate with audit tools.
Vulnerability Assessment
Regular, in-depth risk assessments and vulnerability scans; continuous improvement of security controls; and documented remediation processes.
3) Customer Service : Consent Management
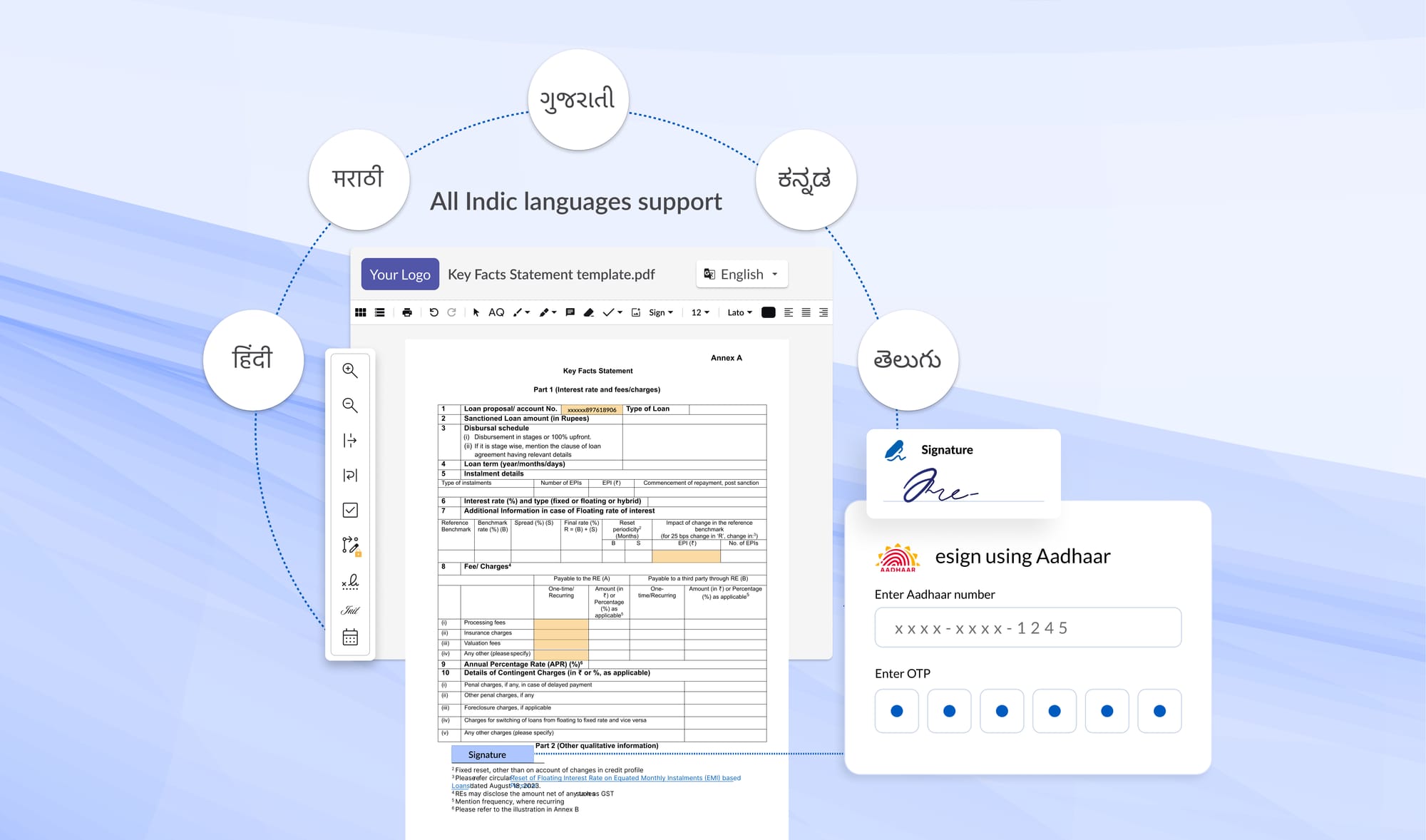
Privacy Notices: Clear notices detailing what personal data is collected, how it is processed, and for what purposes; displayed in the customer’s preferred language
Purpose Mapping: Comprehensive documentation of each data processing activity, tied explicitly to its lawful basis and intended purpose.
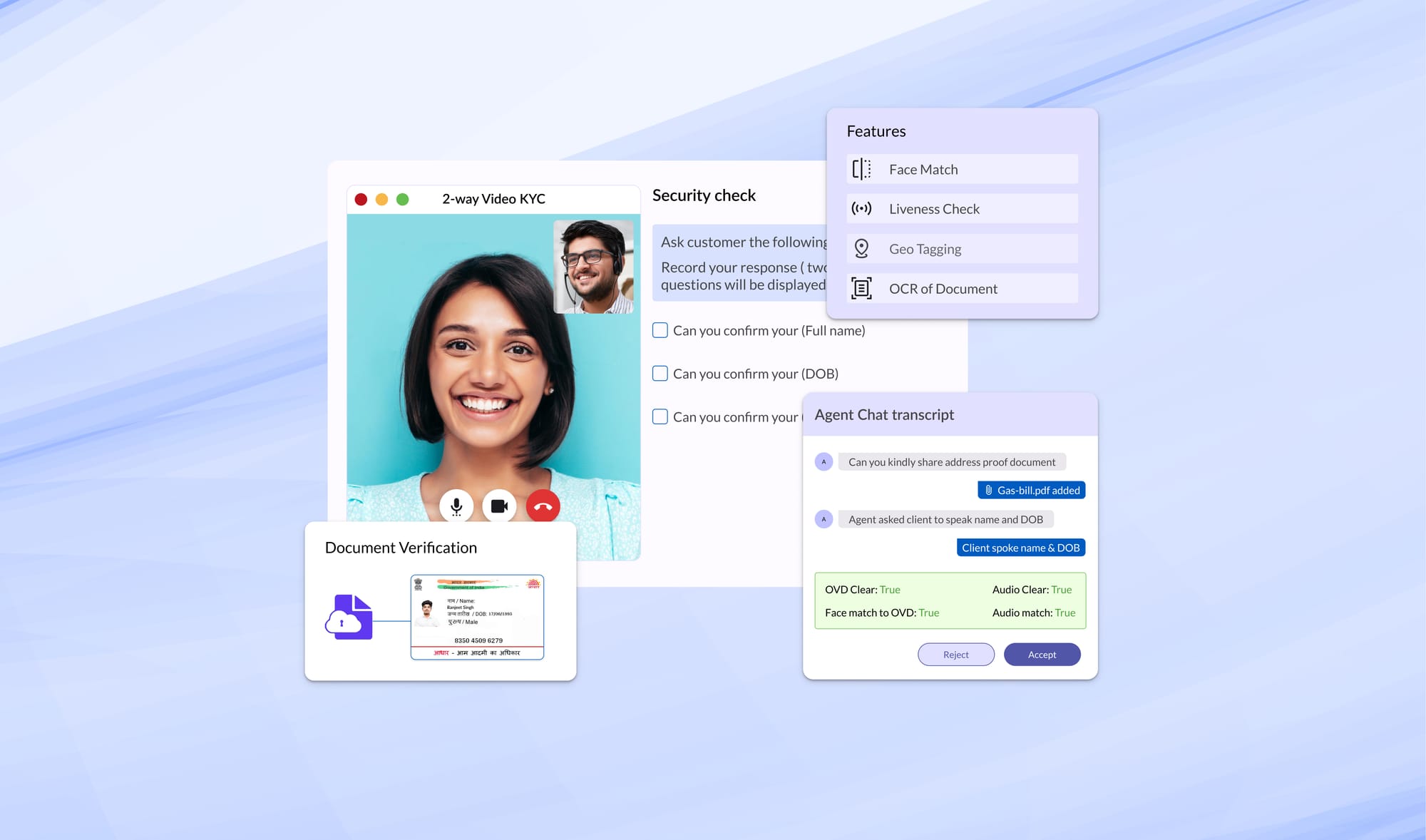
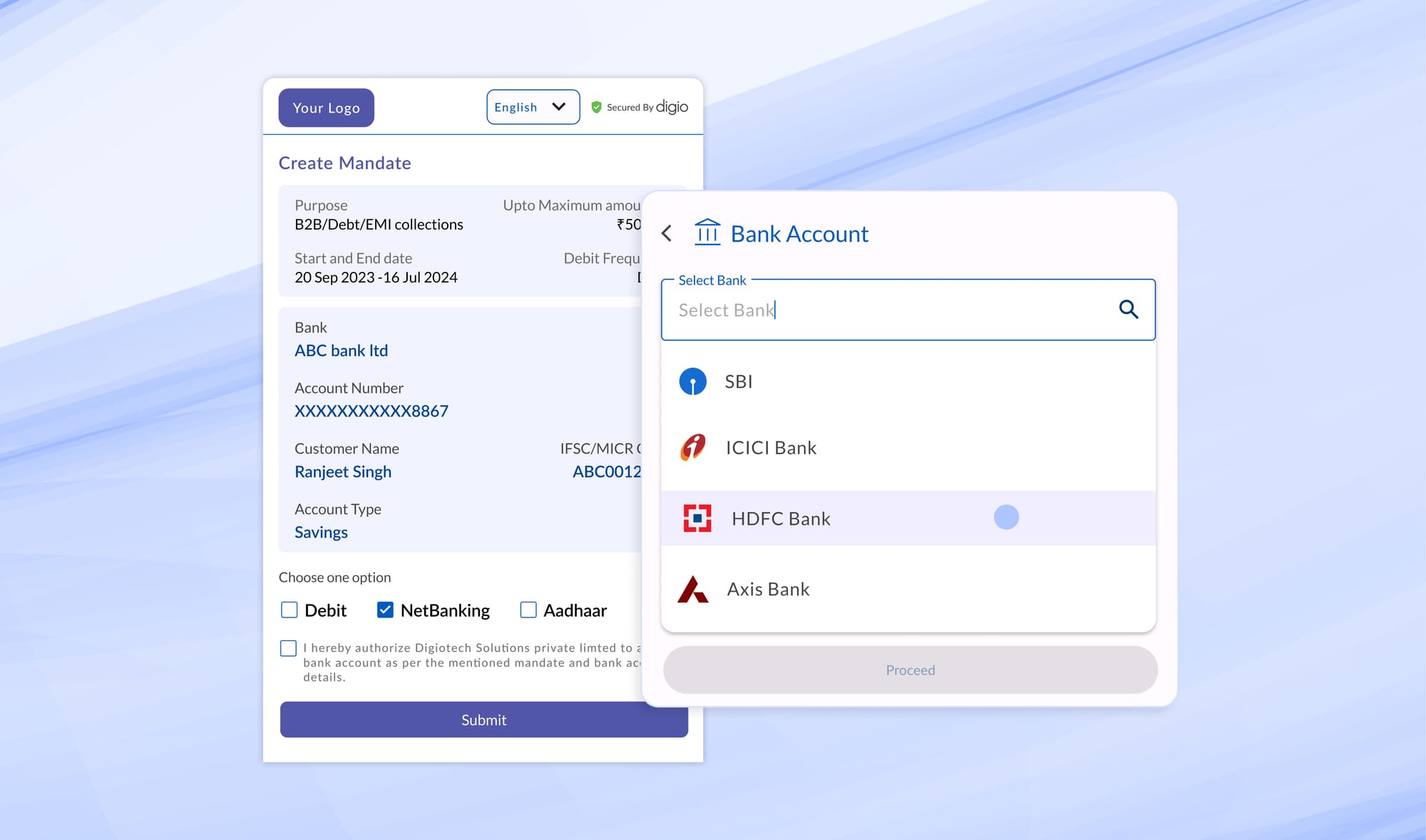
Consent Workflows: Automated processes for customer consents - requesting, tracking, and enforcing data subject rights(DSRs) for data access, modification and erasure.
Cookie Manager: Tracking of data attributes that are not necessarily PII, however, can be used to build a detailed profile of a user's interests, preferences, location, device information, session times - all of which can be used for strategies such as retargetting, advertising and price discrimination.
DPDPA : Solving Compliance to build India's Privacy Infrastructure
As an entity regularly engaging with Regulators, Compliance and Infosec teams, we are well equipped in
- Building and maintaining consent architectures that meet regulatory requirements
- Navigating complex integration challenges across diverse organizations
- Creating user experiences that balance security with usability
- Implementing robust governance frameworks for data and consent management
However, we feel some problems are best solved with the right set of hands and where we are adept in compliance technology, we want to work with the best organizations, who understand enterprise problems in Data privacy and security and have solved for it comprehensively.
We are excited to announce a Strategic Partnership with Aurva.io to bring to India the most effective approach to DPDP compliance combining their expertise in Data Security & Privacy and Digio’s capabilities in Consent Governance to build a comprehensive DPDPA Stack for India.
Elephant in the room : Interoperability across consent systems
Interoperability across consent managers is a framework where even the more mature AA ecosystem has struggled to develop mostly coming from the absence of guidelines from the governing body and the regulator. This has resulted in fragmentation of all consent of a customer across different AAs. We see this being absent even in DPDP. From our learnings there should only be two ways to solve this:
- Centralisation through a Consent Registry : Similar to the present CKYC and Sahamati’s Proxy Layer. This would require all consent managers to share all consent metadata to the registry which can be used by other consent managers for a single view of customer consent across companies.
- Decentralisation through a Shared Ledger : Instead of a single central registry, customer consent metadata is stored on a shared ledger using decentralized identifiers (DIDs) and verifiable credentials. When an end user logs in to a consent manager app, it authenticates the user via secure digital identity to pull non-sensistive consent metadata across consent managers. Any consent updates are relayed across the participants in the ledger to avoid consent fragmentation. The ledger should in principle be maintained by a consortium comprising the data protection board and registered consent manager to ensure the spirit of privacy remains uncompromised and private participation is encouraged to keep ledger maintenance up to date.
Beyond Consent : Building Digital Trust
The ultimate value of DPDP compliance should be to build trust between Data Fiduciaries and Data Principals. This trust is essential for driving economic growth and innovation in the digital economy. We believe through this partnership we want to go beyond mere compliance to enable a trust-based digital asset economy. Stay tuned for more updates. Exciting phase ahead!
Image sources : Niti Aayog - DEPA
Read more Blogs
Digitally transform business operations with Digio!
Try first. Subscribe later.
Boost your legal ops efficiency by 80%
Learn how Digio can enhance your business productivity
Get 1-on-1 business use case solutioning
Speak with our business consultants to get a solution walkthrough for your business requirement
Test the APIs
Let your development team test our API suite to understand configurability and product integration
Subscribe
Get the best in industry commercials for your business usecase